
Have you ever experienced the frustration of discovering an unexpected charge on your bank statement for a forgotten gym membership? Perhaps you kept it active “just in case” you wanted to exercise someday. Similarly, always-on privileged access, also known as “standing privileges,” can lead to similar challenges.
Surprisingly, 77% of organizations provide unrestricted access to employees who do not require it. However, maintaining an always-on approach does not necessarily facilitate their work; instead, it creates opportunities for security breaches that can go unnoticed. In fact, in 2022 alone, 55% of organizations fell victim to cyber-attacks where hackers exploited privileged credentials, a critical attack vector as identified by Verizon.
This article explores the concept of just-in-time (JIT) permission management, its significance in providing the necessary security and efficiency for access control in organizations. We will delve into various types of JIT management, including automated JIT, and discuss the best practices for its implementation within your business.
Related Video: Finding Security Issues Before They Find You
Understanding Just-In-Time (JIT) Permission Management
JIT, also known as just-in-time access, is a cybersecurity practice that adheres to the principle of least privilege. It grants users access to resources, such as applications and systems, only for a limited period when it is specifically needed. Once the designated time expires, users lose access to these resources. This methodology not only limits a user’s access timeframe but also reduces the chances of attackers infiltrating your cloud security perimeter.
With the increasing number of applications, services, users, and resources in the cloud, 45% of breaches in 2022 were cloud-based, making JIT an essential requirement. While traditional privileged access management (PAM) processes, such as session management, are effective for on-premises environments, JIT is particularly suitable for controlling access across cloud resources.
Types of JIT Permission Management
JIT permission management can be implemented in different ways, including:
1. Ephemeral: This approach involves creating a one-time account to fulfill the user’s access requirements, which is then disabled or deleted.
2. Temporary: Users can request elevated privileges on their existing accounts when necessary.
3. Justification-based: Users must provide a valid justification for requiring privileged access, based on predetermined policies. A privileged account and credentials are created and rotated using a central vault in this “broker and remove” access model.
The Importance of Automated Just-In-Time Access
Managing JIT permissions manually can be akin to playing a never-ending game of whack-a-mole, with constant access requests popping up across your organization. Can you realistically allocate sufficient time and personnel to grant and revoke access throughout the day, especially considering the resource constraints faced by 59% of organizations that struggle to deploy zero trust?
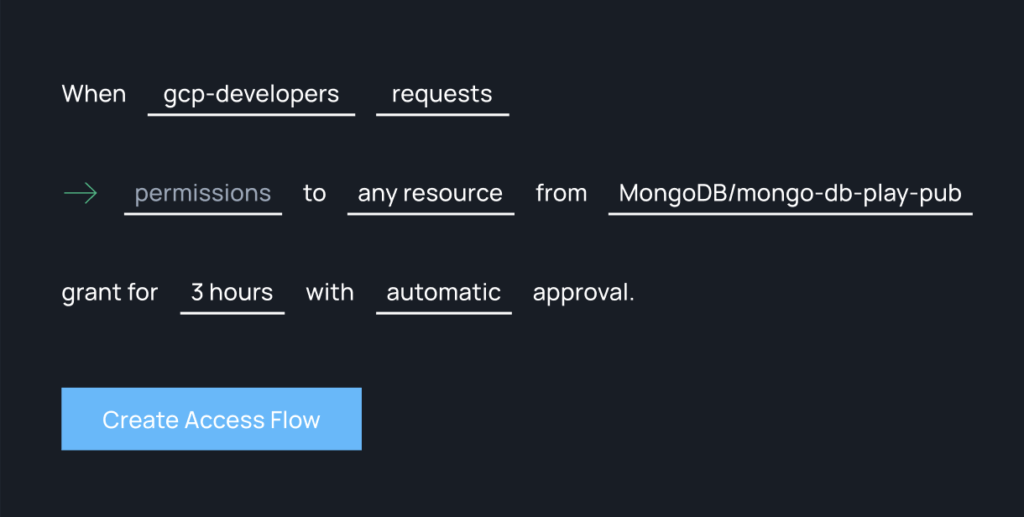
In contrast, automated JIT platforms alleviate the challenges posed by manual permission management. These platforms validate, monitor, and revoke access without requiring human intervention. By offering features such as auto-expiring permissions and comprehensive reporting capabilities, automated JIT platforms empower users to self-serve permission requests while maintaining your organization’s security posture. Entrusting permission management to an automated JIT platform minimizes human error, reduces the attack surface, eliminates bottlenecks, and ultimately preserves productivity.
Benefits of Automated JIT
Automated JIT not only eases the burden on your IT and security teams but also provides several other advantages:
1. Enhanced security posture: Compromised or stolen credentials were the most common attack vector in 2022, according to IBM’s Cost of a Data Breach report. By eliminating the need for standing privileges, automated JIT significantly reduces the risk of privilege abuse and breached identities.
2. Improved business productivity: With an automated JIT approval workflow, you can bid farewell to manual review cycles, waiting times, and human error. You can grant access at scale, tailored to specific tasks, significantly improving operational efficiency.
3. Compliance adherence: Automated JIT enables you to meet compliance and customer requirements, such as SOC2, by enforcing zero trust and least privilege access. These platforms include auditing and reporting features that provide visibility into all sessions and privileges, ensuring compliance with regulations like SOC2 and PCI-DSS.
Enabling JIT Access: Best Practices
To successfully enable and implement JIT access, consider the following best practices:
1. Identify and inventory: Begin by identifying the accounts and assets with the most privileges, particularly those belonging to administrators, which pose the highest risk. Implement JIT access control for these accounts first and then gradually extend it throughout the organization.
2. Use RBAC and ABAC: Utilize role-based access control (RBAC) and attribute-based access control (ABAC) as supplementary solutions to define granular policies and circumstances for elevated access. Categorize accounts, differentiate their rights, and create control policies that users must satisfy to gain access.
3. Define and enable temporary access: Apart from justification-based access, establish criteria for users requesting temporary access, including which accounts are eligible and the duration of access. Implement time-based controls, such as granting access to specific resources during predefined days and times.
4. Record and audit activity: An automated access management solution enables you to log all access activities, receive alerts for suspicious behavior, and record JIT privileged access. Maintaining a comprehensive digital paper trail is essential for auditing, governance, and compliance with regulations such as SOC2 and PCI-DSS.
5. Assign responsibility: Delegate responsibilities to employees and determine who will review permission requests. Properly training employees on granting and revoking access, especially during critical incidents like “break glass” and “on-call” situations, minimizes the risk of incidents. Automated JIT facilitates configuring access flows for these scenarios, helping resolve incidents promptly and eliminating bottlenecks.
6. Use short-lived (ephemeral) credentials: Regularly rotate credentials manually to invalidate them, preventing hackers from exploiting stolen passwords. Employ a centralized vault with the highest level of security clearance to manage these credentials effectively.
7. Employ an automated access management tool: Simplify cloud access management by leveraging solutions like Apono, which enforces an automated JIT approach. By using such tools, you can streamline processes, reduce over-privileges, and ensure that permissions are never overlooked, safeguarding your organization from unnecessary risks.




