Before diving into IoT security risk, let’s make a quick recap: The invention of the internet and its subsequent applications for online-based technology have drastically changed our understanding of digital tech. The implementation of Wi-Fi connected devices has led to the birth of concepts like ‘IoT’.
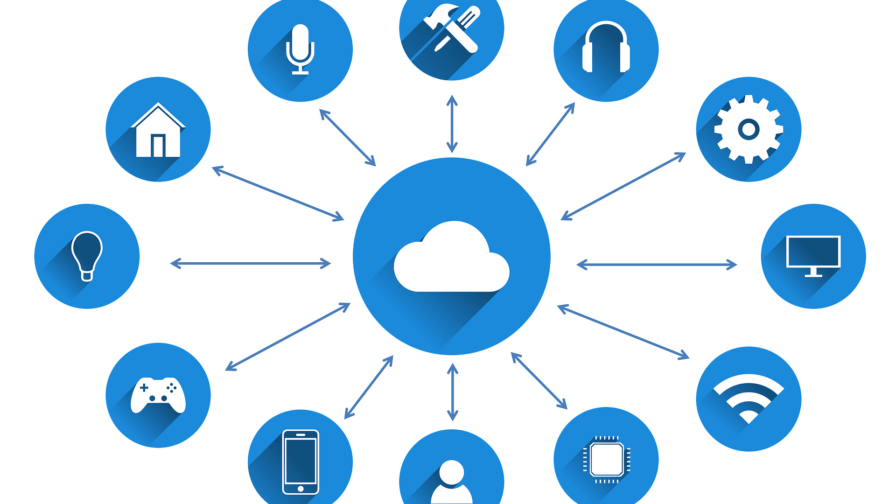
IoT, also known as ‘the Internet of Things”, is a concept used by technology experts to describe how interconnected smart devices and everyday objects are linked to each other via the internet, continually exchanging and synchronizing data.
This is possible thanks to the implementation of D2D connectivity, also known as device-to-device communication, a series of protocols that allows objects to connect via Wi-Fi.
The term was first coined by British technology expert Kevin Ashton, the co-founder of The Procter & Gamble Company (commonly referred to as ‘P&G’). According to Ashton, the Internet of Things describes a moment in time where “more things are connected to the Internet than people”.
Such a statement may seem bold and audacious, but the reality is that IoT has become the new norm. According to industry experts like Transforma Insights, the amount of smart IoT devices has rapidly increased in the past few years. In 2019, there were a total of 7.6 billion IoT smart devices in the world. That number is only expected to increase, reaching 20 billion by 2030.
Although this technology was conceived to make our lives easier, IoT threats, security breaches, and cyberattacks have dramatically risen in the past decade. In August of 2019, for example, a Russian hacker group known as ‘Strontium’ used IoT connected devices like wireless printers to bypass safety protocols and gain access to sensitive networks.
Even though these attacks were not fruitful, the group has carried out many other cyberterrorist operations. In 2016, Fancy Bear, a cell of Strontium, was linked to a string of hacking incidents that targeted the 2016 US presidential election.
As evidenced by these real-life examples, the problem with IoT comes with poorly secured IoT devices that are not built or designed as possible ports of entry to the internet. These devices might be connected via Wi-Fi, but they’re not prepared to withstand any possible hacking attempts.
As a result, one poorly secured device could compromise an entire network of shared data, causing a domino effect that could take down whole corporations.
All of this sounds scary, we know. But with a proper strategy to address IoT security risks, IoT technology is not only useful but also necessary in this day and age. Luckily, we’ve compiled some simple tips to help you develop a robust plan that keeps those dangerous hackers at bay.
And now, without any more delay, here are seven ways to keep your IoT connected company safe.
Hire the hackers
Yes, you read that right. You can avoid hackers by hacking yourself and beating them to it. It may sound like something out of a James Bond film, but many hackers offer their services as cybersecurity experts. Sadly, the term ‘hacker’ has been stigmatized by media and popular culture.
In reality, a hacker is simply a computing and coding expert with experience in breaches and cybersecurity. Within the hacking community, ethical hackers are usually referred to as ‘white hats’. These experts can be a great addition to an IT team, and companies like Google, Netflix, and Apple trust them with their cybersecurity. Remember, not all hackers are criminals.
Follow PCI security standards
PCI stands for ‘payment card industry’. With the expansion of online shopping and eCommerce businesses, the PCI data security standards (DSS) were created as a series of guidelines to protect both companies and customers. When followed, these instructions ensure card data safety (one of the most common IoT risks is credit card data theft).
Although these guidelines regarding PCI compliance are not mandatory by law, they’re generally seen as an essential aspect of digital transactions on the internet. To be PCI DSS compliant, companies should ensure cardholder data encryption as well as two-fold protection.
To avoid IoT risks, any eCommerce company must include these standards as part of their retail cybersecurity measures.
Turn the cloud into a fortress
According to sources like Flexera, 93% of companies implemented cloud computing processes in 2020. Additionally, out of that vast majority of businesses, 87% used a hybrid cloud strategy, mixing public and private cloud services. However, both public and private clouds can be vulnerable to cyberattacks.
Although cloud hosting is relatively safe, Statista claims that in the past 15 years, data breaches have significantly increased, from 157 million in 2005 to 1.5 billion in 2019. As evidenced by those numbers, cloud security breaches are almost 10 times more common than they used to be.
For this reason, implementing data protection in the cloud has become a priority for most corporations. In the years ahead, cloud-based companies should expect more and more cloud-breaching-attempts.
As a result, cloud security standards will become more rigid and exhaustive. Most of these cloud-related incidents, however, are caused by recurring cloud security mistakes.
Here are three of the main flaws that tend to cause IoT breaches:
Poor server maintenance
Not patching or scanning servers periodically can lead to vulnerable cloud services.
Being unaware of zombie servers
In most cases, IoT cyberattacks are aimed at so-called ‘zombie servers’ – inactive or outdated servers that are still connected to active networks and the cloud. Zombie servers are harmful because they act as an open door for malicious hackers.
Weak encryption
In the unlucky event of a data breach, it’s essential to encrypt all sensitive information that could be used in criminal activities. Additionally, many storage companies make the mistake of not deleting data from former customers. This mistake is not only reckless but can be also used as incriminatory evidence in a potential lawsuit.
Network segmentation
VoIP (voice over internet protocol) phones are generally regarded as useful tools that can help companies to improve software development team communication. Although VoIP phones offer many advantages when compared to old-fashioned legacy phones, this online-based means of communication can be subject to harmful cyberattacks.
Let’s try to explain what all this means with a simple visualization exercise. Imagine your communication network as one big house of cards. One successful strike could take down the entire structure.
Now imagine different, smaller, more robust houses of cards spread out along multiple surfaces. If one were to fall, the others could still carry on working as if nothing had happened.
If at this point you’re questioning what any of this has to do with VoIP phones, just ask yourself: “what is a VoIP phone?”. When you give it some thought, a VoIP connection is a device used to establish a virtual phone line that connects callers via the internet.
As with any other IoT connected device, VoIP phones can be vulnerable to hacking and cyberattacks, potentially leading to major security breaches. For this reason, it’s important to implement segmentation strategies within a VoIP network. Then, in the unlikely event of a successful hacking attempt, the entire network is not compromised.
Rethink the recruitment process
As we mentioned before, a new breed of IT experts like ethical hackers and white hats have risen to the occasion as very in-demand cybersecurity professionals in the IoT industry. Adding these new profiles to your team will undoubtedly help you to mitigate risks.
However, training new talent from different departments during their first steps in your company is equally important. Every successful candidate that joins your team should have some basic notions of IoT safety.
Everybody, from sales representatives to HR and customer service experts, could accidentally cause a cybersecurity breach. Teaching basic security protocols, according to their respective fields of work, should be your first step after adding new talent to your roster.
In this day and age, most recruits and remote workers possess fundamental IT skills. Although everybody seems to know basic stuff like how to send a fax via email, not every employee understands what a firewall is or how data encryption works.
For this reason, organizing webinars and training programs for new workers is a good course of action when developing strategies to reduce IoT related risks.
These courses can be planned remotely and should include different levels and modules. Thanks to the rapid development of video conferencing tools, trainees should be able to learn these skills as long as they have access to a stable internet connection and know how to screen share and follow tutorials or live sessions.
It’s that simple: you don’t need a big infrastructure to make the most out of hardworking and talented newcomers, just access to the online world and all of its possibilities.
Adjust your budget
At this point, it should probably go without saying, but all of these IoT risk mitigation strategies won’t make any difference if your company doesn’t make the appropriate investments to put these measures in motion.
However, we understand that smaller eCommerce businesses may not have the biggest budget, so for this reason, it’s important to scout what products and services fit your needs the best before throwing money at the first anti-malware or spyware firewall you find on the internet.
Matching your cybersecurity to your company’s size and requirements is a long and arduous process. But we can assure you that investing in the best enterprise network security protocols will pay dividends in the long run.
Another option for those businesses that lack expertise or simply don’t have the time to go through this process is hiring third-party cybersecurity consultants. These professional B2B cybersecurity experts only purpose is to find the best products for their clients.
Additionally, many cybersecurity consultors offer their own risk assessment and security protocol services.
Implement MDM measures
In the wake of the COVID-19 pandemic, most companies have been forced to send their workers home. This compulsory switch to remote working and telecommuting has opened the doors for possible new IoT issues. Thankfully, MDM (mobile device management) can help IT teams to solve cybersecurity breaches as well as any other type of problem remotely and quickly.
Mobile device management allows IT experts to take control over their partners’ devices. This approach to remote problem solving not only keeps your staff connected and your IoT smart-devices safe but also reduces the risks that come with BYOD policies.
BYOD (bring your own device) is an increasingly popular strategy for eCommerce businesses that has become widely relied upon during these unprecedented times. With most of the workforce working from home, many companies have reduced costs by letting staff members use their own laptops, tablets, and smartphones as working tools, rather than supplying them with corporate devices.
Although this strategy makes sense from a financial standpoint, it can cause certain IoT related troubles. If your employee’s laptop is attacked by ransomware or spyware viruses, that security breach could end up directly impacting your company, since the device is linked to your cloud and business data.
This not only puts your company at risk but could also put your clients’ sensitive intel on the line. Thankfully, MDM lets IT cybersecurity experts solve these problems as fast as possible in a remote manner.
Conclusios: Mitigate IoT Security Risk
As we’ve seen, IoT technology is not inherently dangerous, but hackers with criminal intentions are. The Internet of Things is a helpful tool that boosts productivity and makes things easier in the workspace, but in the wrong hands or used by inexperienced workers, it can lead to leaks or attacks.
These risks can be reduced and mitigated by applying the above strategies. Every company and industry is in touch with IoT-connected devices. From healthcare in hospitals or retirement homes to schools or transport companies. Any business, even those not directly associated with IT, can be subject to attacks.
The problem with IoT comes when devices or objects are not inherently designed to be connected to via Wi-Fi. For example, the boating industry is especially vulnerable to IoT related attacks. But cars, printers, fridges, and video game consoles are no different.
Thankfully, whether you’re an IT related company or simply a small business getting into IoT devices, these tips will help you to keep your business and your clients safe.




